Enhanced RC5 Algorithm using Parallel Computing for Communication Networks
Main Article Content
Keywords
Cryptography, symmetric key, RC5, algorithm, performance
Abstract
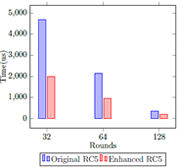
One of the main disadvantages of symmetric key algorithms in comparison with asymmetric key ones is their lower security level due to their shorter key length. Indeed, increasing the number of bits that conforms the key used by a symmetric cryptography algorithm will increase its security level with a cost on its performance. Expanding a key in symmetric cryptography is not an easy task due to algorithms are designed to work with keys of a fixed maximum length. This paper presents an alternative design of the RC5 cryptography algorithm with an enhanced security level achieved through a key expansion mechanism with Parallel Computing processing. Although the design was created for the RC5 algorithm the main idea might be applied to other block cipher algorithms applying the same criteria. This methodology makes feasible to obtain a robust symmetric key algorithm implemented in software with an acceptable performance in comparison with other techniques such as implementations in hardware, reduction in the amount of data, improvements in the key exchange process, advanced high performance computing, and many others techniques.
Downloads
References
[2] J. S. Coron, “What is cryptography?” IEEE Security and Privacy, 2006. [Online]. Available: https://doi.org/10.1109/MSP.2006.29
[3] S. Chandra, S. Paira, S. S. Alam, and G. Sanyal, “A comparative survey of symmetric and asymmetric key cryptography,” 2014 International Conference on Electronics, Communication and Computational Engineering, ICECCE 2014, pp. 83–93, 2014. [Online]. Available: https://doi.org/10. 1109/ICECCE.2014.7086640
[4] J. N. Gaithuru, M. Bakhtiari, M. Salleh, and A. M. Muteb, “A comprehensive literature review of asymmetric key cryptography algorithms for establishment of the existing gap,” 2015 9th Malaysian Software Engineering Conference, MySEC 2015, pp. 236–244, 2016. [Online]. Available: https://doi.org/10.1109/MySEC.2015.7475227
[5] A. Mirtalebi and S. M. Babamir, “A cryptography approach on security layer of web service,” Application of Information and Communication Technologies, AICT 2016 - Conference Proceedings, 2017. [Online]. Available: https://doi.org/10.1109/ICAICT.2016.7991698
[6] S. Vyakaranal and S. Kengond, “Performance Analysis of Symmetric Key Cryptographic Algorithms,” 2018 International Conference on Communication and Signal Processing (ICCSP), pp. 411–415, 2018.
[7] B. Mandal, S. Chandra, S. S. Alam, and S. S. Patra, “A comparative and analytical study on symmetric key cryptography,” 2014 International Conference on Electronics, Communication and Computational Engineering, ICECCE 2014, pp. 131–136, 2014. [Online]. Available: https://doi.org/10. 1109/ICECCE.2014.7086646
[8] M. Peyravian and D. Coppersmith, “Structured symmetric-key block cipher,” Computers and Security, vol. 18, no. 2, pp. 134–147, 1999. [Online]. Available: https://doi.org/10.1016/S0167-4048(99)90053-6
[9] N. Bajaj and A. Thakur, “Enhancement of RC5 for image encryption,” ICIIP 2011 - Proceedings: 2011 International Conference on Image Information Processing, vol. 2, no. Iciip, pp. 7–11, 2011. [Online]. Available: https://doi.org/10.1109/ICIIP.2011.6108973
[10] W. Changda and J. Shiguang, “Multilevel security model for ad hoc networks,” Journal of Systems Engineering and Electronics, vol. 19, no. 2, pp. 391–397, 2008. [Online]. Available: https://doi.org/10.1016/ S1004-4132(08)60098-5
[11] T. Nie, Y. Li, and C. Song, “Performance evaluation for CAST and RC5 encryption algorithms,” 2010 International Conference on Computing, Control and Industrial Engineering, CCIE 2010, vol. 1, pp. 106–109, 2010. [Online]. Available: https://doi.org/10.1109/CCIE.2010.34
[12] O. Elkeelany and S. Nimmagadda, “Performance Evaluation of Differente Hardware Models of RC5 Algorithm,” ICIIP 2011 - Proceedings: 2011 International Conference on Image Information Processing, pp. 142–145, 2007.
[13] I. A. Kamil and S. O. Ogundoyin, “An improved certificateless aggregate signature scheme without bilinear pairings for vehicular ad hoc networks,” Journal of Information Security and Applications, vol. 44, pp. 184–200, 2019. [Online]. Available: https://doi.org/10.1016/j.jisa.2018.12.004
[14] N. B. Silva, D. F. Pigatto, P. S. Martins, and K. R. Branco, “Case studies of performance evaluation of cryptographic algorithms for an embedded system and a general purpose computer,” Journal of Network and Computer Applications, vol. 60, pp. 130–143, 2016. [Online]. Available: http://dx.doi.org/10.1016/j.jnca.2015.10.007
[15] S. O’Melia and A. J. Elbirt, “Instruction set extensions for enhancing the performance of symmetric-key Cryptography,” Proceedings - Annual Computer Security Applications Conference, ACSAC, pp. 465–474, 2008. [Online]. Available: https://doi.org/10.1109/ACSAC.2008.10
[16] M. Mozaffari-Kermani and A. Reyhani-Masoleh, “Efficient and highperformance parallel hardware architectures for the AES-GCM,” IEEE Transactions on Computers, vol. 61, no. 8, pp. 1165–1178, 2012. [Online]. Available: https://doi.org/10.1109/TC.2011.125
[17] L. Hua, L. Jianzhou, and Y. Jing, “An efficient and reconfigurable architecture for RC5,” Canadian Conference on Electrical and Computer Engineering, vol. 2005, pp. 1652–1655, 2005. [Online]. Available: https://doi.org/10.1109/CCECE.2005.1557299
[18] A. J. Elbirt and C. Paar, “An instruction-level distributed processor for symmetric-key cryptography,” IEEE Transactions on Parallel and Distributed Systems, vol. 16, no. 5, pp. 468–480, 2005. [Online]. Available: https://doi.org/10.1109/TPDS.2005.51
[19] Y. Yifeng, G. Yong, W. Heyu, and L. T. School, “A Symmetric Key Exchange Protocol Bsaed on Virtual S-Box,” China Communications, vol. 11, no. 14, p. 5522, 2014.
[20] R. S. Kumar, E. Pradeep, K. Naveen, and R. Gunasekaran, “Enhanced cost effective symmetric key algorithm for small amount of data,” 2010 International Conference on Signal Acquisition and Processing, ICSAP 2010, pp. 354–357, 2010. [Online]. Available: https://doi.org/10.1109/ICSAP. 2010.13
[21] T. Teerakanok and S. Kamolphiwong, “Accelerating asymmetric-key cryptography using Parallel-key Cryptographic Algorithm (PCA),” 2009 6th International Conference on Electrical Engineering/Electronics, Computer, Telecommunications and Information Technology, pp. 812–815, 2009. [Online]. Available: https://doi.org/10.1109/ECTICON.2009.5137170
[22] C. Negre and J. M. Robert, “New parallel approaches for scalar multiplication in elliptic curve over fields of small characteristic,” IEEE Transactions on Computers, vol. 64, no. 10, pp. 2875–2890, 2015. [Online]. Available: https://doi.org/10.1109/TC.2015.2389817
[23] P. Bilski and W. Winiecki, “Multi-core implementation of the symmetric cryptography algorithms in the measurement system,” Measurement: Journal of the International Measurement Confederation, vol. 43, no. 8, pp. 1049–1060, 2010. [Online]. Available: http://dx.doi.org/10.1016/j. measurement.2010.03.002
[24] A. Amerimehr and M. H. Dehkordi, “Quantum Symmetric Cryptosystem Based on Algebraic Codes,” IEEE Communications Letters, vol. 22, no. 9, pp. 1746–1749, 2018. [Online]. Available: https://doi.org/10.1109/LCOMM. 2018.2844245
[25] J. P. Aumasson, “The impact of quantum computing on cryptography,” Computer Fraud and Security, vol. 2017, no. 6, pp. 8–11, 2017. [Online]. Available: http://dx.doi.org/10.1016/S1361-3723(17)30051-9
[26] H. A. Kholidy, A. A. Azab, and S. H. Deif, “Enhanced "ULTRA GRIDSEC": Enhancing high performance symmetric key cryptography schema using pure peer to peer computational grid middleware (HIMAN),” 2008 3rd International Conference on Pervasive Computing and Applications, ICPCA08, vol. 1, pp. 26–31, 2008. [Online]. Available: https://doi.org/10. 1037/h0094584
[27] J. Liang, Q. Wang, Y. Qi, and F. Yu, “An area optimized implementation of cryptographic algorithm RC5,” 2009 5th International Conference on Wireless Communications, Networking and Mobile Computing, pp. 4–7, 2009.
[28] E. B. Villanueva, R. P. Medina, and B. D. Gerardo, “An enhanced RC5 (ERC5) algorithm based on simple random number key expansion technique,” ISCAIE 2018 - 2018 IEEE Symposium on Computer Applications and Industrial Electronics, vol. 5, pp. 134–138, 2018. [Online]. Available: https://doi.org/10.1109/ISCAIE.2018.8405458
[29] M. Sharafi, F. Fotouhi-Ghazvini, M. Shirali, and M. Ghassemian, “A low power cryptography solution based on chaos theory in wireless sensor nodes,” IEEE Access, vol. 7, no. c, pp. 8737–8753, 2019. [Online]. Available: https://doi.org/10.1109/ACCESS.2018.2886384